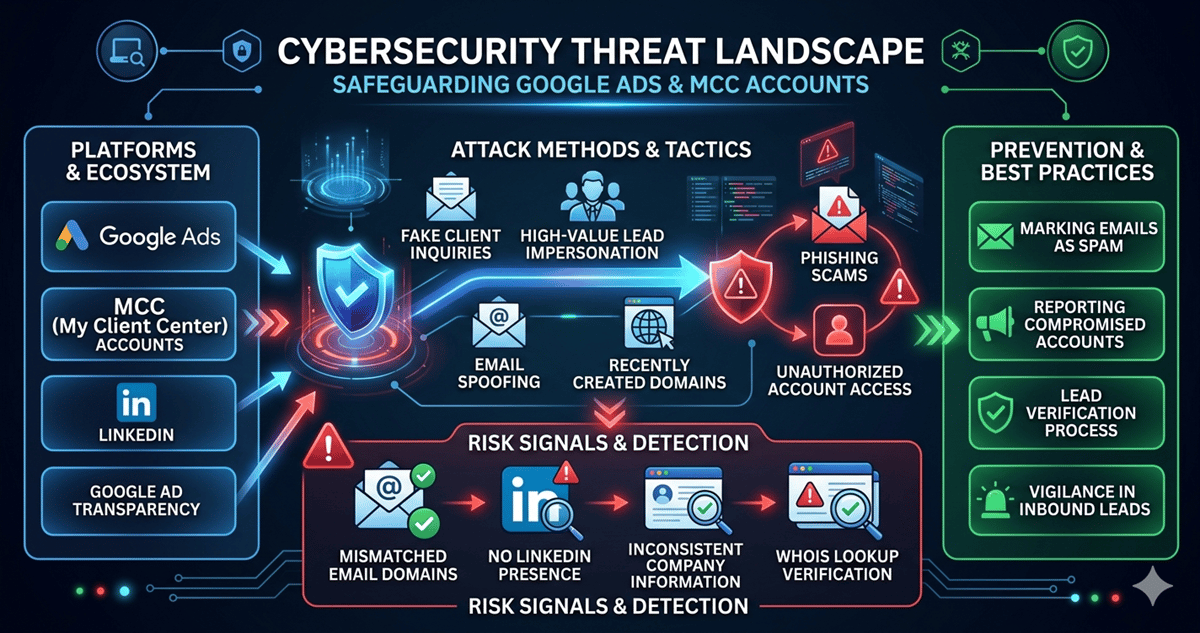
In the world of digital advertising, every new inquiry feels like opportunity knocking. But lately, some of those knocks aren’t coming from potential clients—they’re coming from intruders dressed as opportunity. The recent wave of phishing attacks targeting Google Ads accounts is a reminder that not every lead is what it seems.
Think of your agency like a well-run storefront. You’ve invested in visibility, reputation, and trust. Now imagine someone walks in, perfectly dressed, speaking your language, asking all the right questions. You’d welcome them in. That’s exactly how these phishing attacks work—they don’t break the door down, they get invited inside.
According to Ginny Marvin, while platforms actively monitor suspicious activity, the first line of defense still sits with advertisers. Marking suspicious emails, reporting compromised accounts, and staying alert are no longer optional—they’re operational hygiene.
The Trojan Horse Lead
Pauline Jakober recently shared a near miss that perfectly illustrates this evolving threat. Her agency received what looked like a high-value inbound lead—a global brand, polished communication, everything aligned.
But this wasn’t a client. It was a Trojan horse.
At first glance, everything checked out. The website looked legitimate. The inquiry felt real. But as Jakober dug deeper, subtle cracks began to appear:
The email address didn’t match the sender’s domain
The person had no credible presence on LinkedIn
Follow-up responses contained inconsistent company details
Domain records showed the website was only days old
What looked like a premium opportunity was actually a carefully constructed entry point—designed to gain access to high-value ad accounts like MCC (My Client Center).
Phishing Has Grown Up
This isn’t the old version of phishing filled with broken grammar and obvious red flags. Today’s attackers are marketers in their own right. They understand targeting, personalization, and trust signals.
They mimic:
Enterprise-level clients
Clean brand identities
Professional communication flows
In short, they’ve learned from the very ecosystem they’re attacking.
The result? Agencies are no longer just managing campaigns—they’re managing risk at every entry point.
Your Pipeline Is Also Your Perimeter
Here’s the uncomfortable truth: your lead funnel is now part of your security system.
Every form fill, every inbound email, every “new opportunity” is a potential access request—not just to your services, but to your infrastructure.
That means the qualification process needs to evolve from:
“Is this a good client?”
to
“Is this even a real client?”
The best agencies are already shifting their mindset. They treat inbound leads not just as revenue potential, but as identity verification exercises.
Actionable Takeaway: Build a “Zero-Trust” Lead Process
To protect your accounts without slowing down growth, implement a simple rule: trust nothing without validation.
Here’s what that looks like in practice:
Verify identity before engagement
Cross-check domains, emails, and company presence across multiple sourcesScrutinize urgency and scale
High-budget, fast-moving inquiries deserve extra caution—not excitementCheck digital footprints
Validate individuals via platforms like LinkedIn, company sites, and Whois dataSeparate access from conversation
Never grant account-level access early in discussionsTrain your team to spot patterns
Security isn’t a tool—it’s a shared instinct
In a landscape where attackers behave like ideal customers, vigilance becomes a competitive advantage.
Because in today’s market, growth doesn’t just come from saying “yes” to the right clients—it comes from knowing when to say “no” to the wrong ones.
